Streamline visitor management with automated security checks at pre-registration and sign-in. Screen visitors before arrival, review legal documents and watchlist results in advance, and manage on-site entry efficiently with customizable workflows for high-security environments.

Streamline Access with Automated Control
By automating the approval process through a custom configuration, you ensure compliance with regulatory requirements while minimizing manual intervention. This feature protects your facility and streamlines the visitor experience, ensuring only authorized visitors gain access.
ITAR Compliance
Meet International Traffic in Arms Regulations (ITAR) by ensuring that only eligible visitors can access sensitive areas.
Verify Visitor Documentation
Verify that visitors possess the necessary documentation to be on-site, such as citizenship verification for U.S. facilities.
Confirm Visitor Identity
Add a critical checkpoint in the process, allowing facility personnel to verify that the person who signed in matches their identification.
Control Visitor Access
Only approved visitors enter your facility, preventing unauthorized individuals from accessing your premises.
Mitigate High-Risk Access
Watchlist integrations screen visitors during pre-registration and sign-in, identifying high-risk individuals before they enter your facility.
Comprehensive Audit Logs
Track all visitor approvals and denials at both pre-registration and on-site stages. A complete audit log of all status changes provides clear visibility for compliance reporting and accountability.
Pre-Registration Approval
Approve or deny visitors before arrival. Review pre-registration details, screening results, and legal documents before issuing QR codes.



















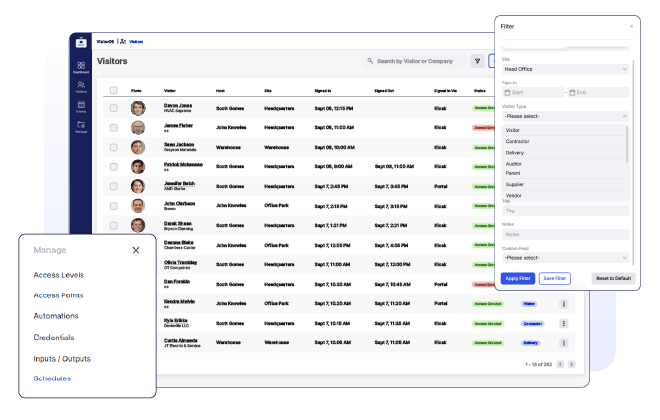
How Visitor Approval Works
Visitor Approval enables organizations to screen and approve visitors before arrival or at sign-in. Review pre-registration details, watchlist screening results, and legal documents, then approve or deny access. Automated workflows and customizable approval criteria help maintain security and compliance across your facility.
Step 1
Configure Approval Settings
Set up approval criteria for different visitor types. Configure workflows for pre-registration and on-site check-ins, designate approvers, and enable Pre-Registration Approval in Site Settings to screen visitors before arrival.

Step 2
Pre-Registration Review (When Enabled)
When a guest completes pre-registration and meets approval criteria, they are marked as "Pre-Registration Pending Approval" and do not receive a QR code. Approvers receive an email to review details and can approve or deny from the side panel.

Step 3
On-Site Validation of Entry
When a guest signs in on-site (who hasn't pre-registered or requires additional approval), VisitorOS automatically sends a request to the designated representative for verification if they meet the predefined criteria. The designated representative will approve or deny the visitor based on your organization's guidelines.

Step 4
Visitor is Approved or Denied Entry
Visitors are approved or denied entry. For pre-registration approvals, approved guests receive a QR code via email; denied guests do not. For on-site approvals, visitors gain immediate access or are denied. Administrators receive email notifications for all denials.

Step 5
The Record is Tracked in the Visitor Log
Every approval and denial are recorded in the visitor log, providing a comprehensive history of who was granted entry to the facility, who was denied entry to the facility, and when.
Who Benefits from Visitor Approval Functionality?
The visitor approval feature is designed for organizations prioritizing facility security and compliance.
Security and Compliance Officers
Security and compliance officers benefit from streamlined processes that help them enforce regulations and maintain a secure environment. The feature provides them with tools to monitor visitor access effectively.
High-Security Environments
Organizations operating in high-security environments can leverage this feature to ensure that only vetted individuals gain entry. This capability is crucial for safeguarding sensitive areas and protecting valuable assets.
Compliance-Certified Industries
Facilities requiring compliance with standards such as ITAR, CGP, and other regulatory certifications benefit significantly from this feature. It aids in meeting stringent requirements while enhancing overall security management.
View Visitor Management Resources
See more resources and tools on the latest trends, technology, and best practices for facility operations.
What Can VisitroOS Do for You?
Request a demo to see how VisitroOS can deliver immediate results for your organization.
Book a Demo